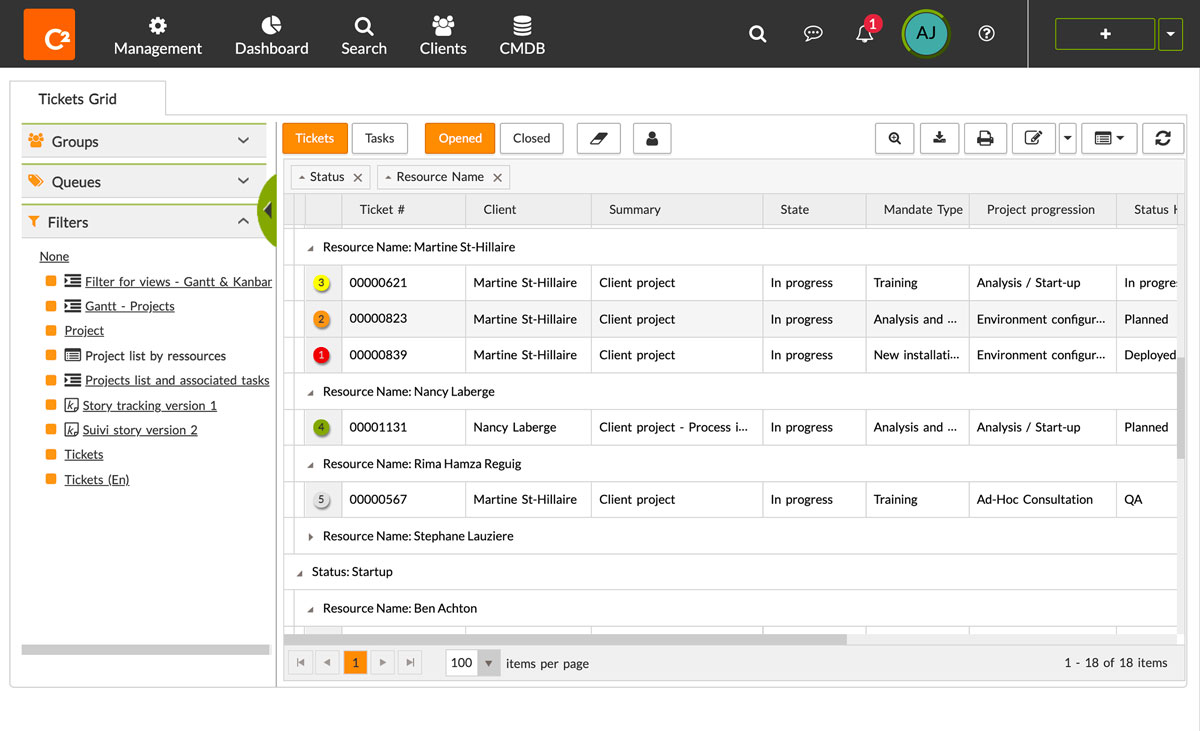
Master your IT service workflows — for good
C2 enables you to serve your customers better through efficient and flexible IT service management.
Request personalized demo
ITSM should be structured, secure and stable. Now it can be.
With a foundation in operational best practices, C2 is an all-in-one IT service management cloud platform that’ll help your teams drive great collaboration, effective delivery and powerful automation. All that without coding—or breaking the bank.
It’s the complete
package
C2 is a comprehensive solution that includes everything you need to set up, configure, and launch your service desk today—with no costly add-ons. And thanks to C2’s advanced customization options, you’ll be able to mold and personalize your platform as you go.

Intuitive service desk
Categorize instantly, manage prioritizations and track time to ease workload.
Self-service portal and catalog
Powerful asset management
Track inventory, assets, licenses, POs and more inside a robust CMDB.
CMDB and asset management
Automated workflows and processes
Escalate, manage workflows, assign tasks, or create and approve custom triggers.
Workflows and automation
Seamless integrations
Connect your favorite apps with APIs and webhook triggers.
Integrations & APIs
Empower your service delivery
Enhance performance and automate workflows for simple or complex processes without a single line of code. Approvals, notifications, escalation, prioritization and beyond, we have you covered. C2 will elevate your productivity and let you focus on value-added tasks.
Workflows and automationBoost your operations
Implement best practices fast to improve agility, drive change management and reduce downtime. Transform the way you work & collaborate efficiently to bring structure to your services.
CMDB and asset managementDelight your customers
Prioritize and centralize requests through a customizable service catalog and a powerful self-service portal, allowing you to deliver higher SLAs. Create one point of entry for your customers and tailor their experience to their needs.
Self-service portal and catalogSynchronize all your tools
C2 is a leader in IT tool integration and helps simplify the way you deliver services and orchestrate all operations from one platform. Easily sync user information and centralize all access. Connect all your systems to standardize horizontal or cross-platform processes.
Integrations and APIs"The extensive versatility of C2, as well as the service management centralization, allowed us to significantly increase the efficiency of all the services for which we are using C2."
Pete Settle
Business System Analyst
Nova Scotia Liquor Corporation
Trusted by private and public organizations





